Posts by bobmadden
Citizen Surveillance
I thought to celebrate Data Privacy Day, held every January 28, I would create a document that will help you understand the constant collection of personal data, how it is…
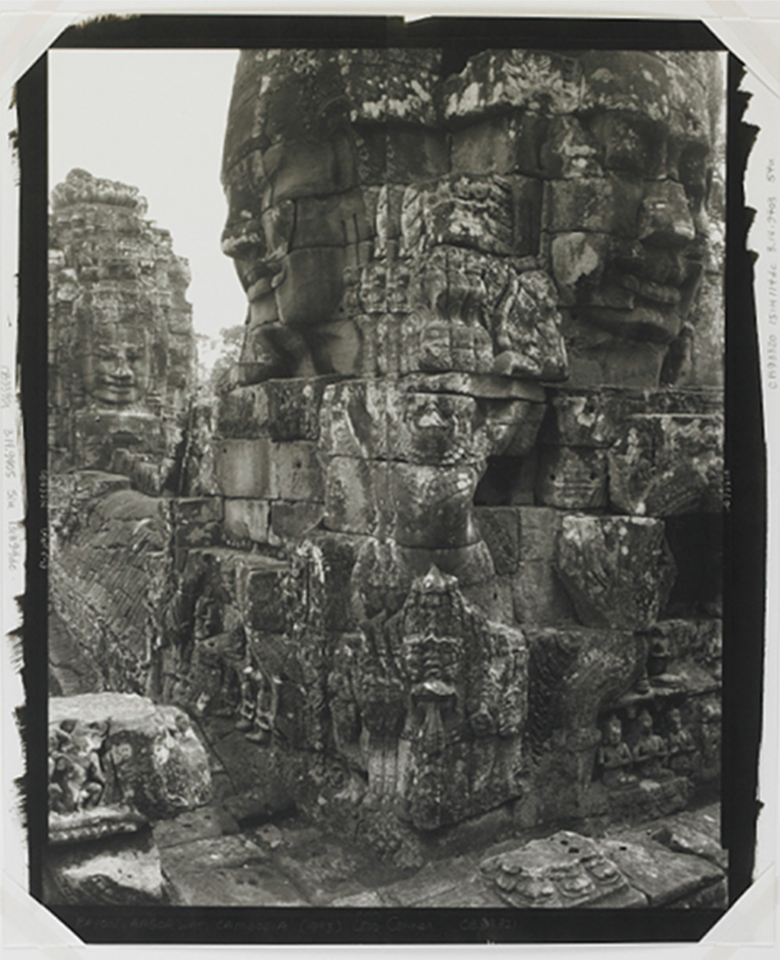
Read More30 Years Ago at National Geographic
Thirty ago this month, I was working for the National Geographic Society (NGS) developing the prototype for a digital photographic archive for the Society’s Image Collection. It was incurring significant…
Read MoreUpdate on My Daily Postings
Three years. That is the timeframe for my visual diary. As my followers on this website, or on my Twitter and Facebook know, every day current images are posted.…
Read MoreArchiving The Freer/Sackler Museums Collection
The Freer/Sackler Museums of Asian Art are a hidden jewel in the Smithsonian complex on the National Mall in Washington, DC. Yearly visitors at the Freer/Sackler number about a half…
Read MoreThe MOMA Exhibit OBJECT:PHOTO
I saw the photographic exhibit “OBJECT:PHOTO at the Museum of Modern Art in New York City. It is essentially the Thomas Walther Collection, a selection of 341 ”modern” photographs by…
Read MoreTweeting My Visual Diary
When Twitter, Now X, first appeared, I felt like many others that I did not need to know how someone I was following was enjoying breakfast. But I began to…
Read MoreLUMIX Gh4: Capturing Stills from 4k video
Recently, I tested a Panasonic LUMIX Gh4 with two important features that affect how still photographers will be capturing images in the near future. Firmware now offered by Panasonic for…
Read MoreInstagram Comments on Martin Luther King Post
On Martin Luther King Day, I posted this Instagram with the following caption” “Monument in Washington DC. An awe-inspiring statue of an extraordinary man. He was killed before the current…
Read MoreReview of My 2014 Blogs
Recently I looked back at the archive of blogs that I posted in 2014. Although there were a couple of outliers, most blogs fit into specific photographic themes. Please click…
Read MoreWhose Land Is It Anyway?
A small bit of history to tether the current phenomena of land acquisition around the world. In 1803, the United States bought what became known as the Louisiana Purchase from…
Read More